Match Following Terms Explanations Defect Bug Flaw Risk Implementation Vulnerabilities B Q43855824
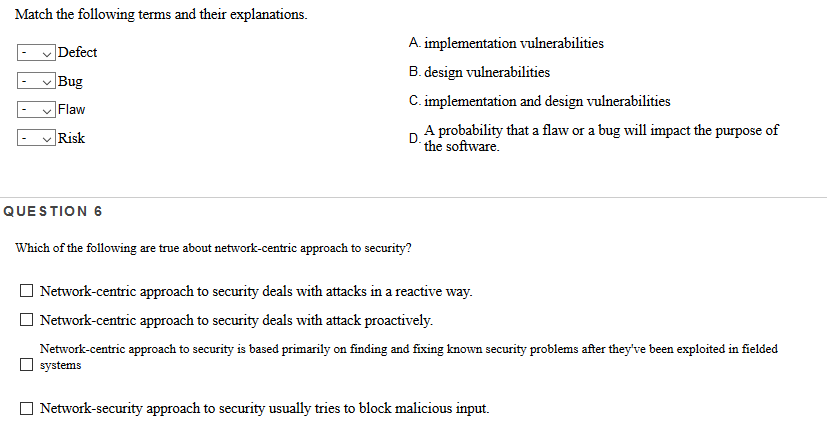
Match the following terms and their explanations. Defect Bug Flaw Risk A. implementation vulnerabilities B. design vulnerabilities C. implementation and design vulnerabilities A probability that a flaw or a bug will impact the purpose of the software. – QUESTION 6 Which of the following are true about network-centric approach to security? Network-centric approach to security deals with attacks in a reactive way. Network-centric approach to security deals with attack proactively. Network-centric approach to security is based primarily on finding and fixing known security problems after they’ve been exploited in fielded systems Network-security approach to security usually tries to block malicious input. Show transcribed image text Match the following terms and their explanations. Defect Bug Flaw Risk A. implementation vulnerabilities B. design vulnerabilities C. implementation and design vulnerabilities A probability that a flaw or a bug will impact the purpose of the software. – QUESTION 6 Which of the following are true about network-centric approach to security? Network-centric approach to security deals with attacks in a reactive way. Network-centric approach to security deals with attack proactively. Network-centric approach to security is based primarily on finding and fixing known security problems after they’ve been exploited in fielded systems Network-security approach to security usually tries to block malicious input.
Expert Answer
Answer to Match the following terms and their explanations. Defect Bug Flaw Risk A. implementation vulnerabilities B. design vulne…
OR